This platform teaches you how to exploit vulnerabilities in hacking operations

To become a professional hacker (we are talking about ethical hackers, of course), this calls for adherence to a long path to learn various techniques related to the field. Such as first getting acquainted with the computer and its components, knowledge about the network and networking, basics about programming, social engineering techniques, reverse engineering and more. However, sometimes someone just wants to learn to hack something specific, such as website penetration testing, Android apps, database hacking, and more. This does not require taking a complete course in the field of hacking, but it is sufficient for you to have the initial basics, and then proceed directly to learning what you want to learn to hack.

We may help you in this topic today to achieve your goal, as we would like to show you a platform on the web that allows you to literally learn to hack anything you want, whether it is hardware or software. It is enough for you to be aware of the initial basics of computers and systems, then follow the explanation provided by this platform, and you will become an expert in hacking.
Hacksplaining time
HackSplaining (an amalgamation of Hack and Explaining) is an excellent platform that allows you to choose one of the most popular vulnerabilities. The site shows you all kinds of vulnerabilities that you are likely to find on specific platforms (websites, applications…), then tells you how this vulnerability was created, to finally explain to you how to search for it, and then how to exploit it in the hacking process.
The site is easy to use, and does not require any registration or login with your account. Once accessed, you will find a list of all the techniques available on the site that he can teach you. Start by choosing what you want to learn, to go to an interactive page that explains to you how the hacking process takes place by means of this vulnerability, then how it can be exploited, and finally how you can protect yourself (or your software) from this vulnerability.
Many loopholes and many techniques to learn
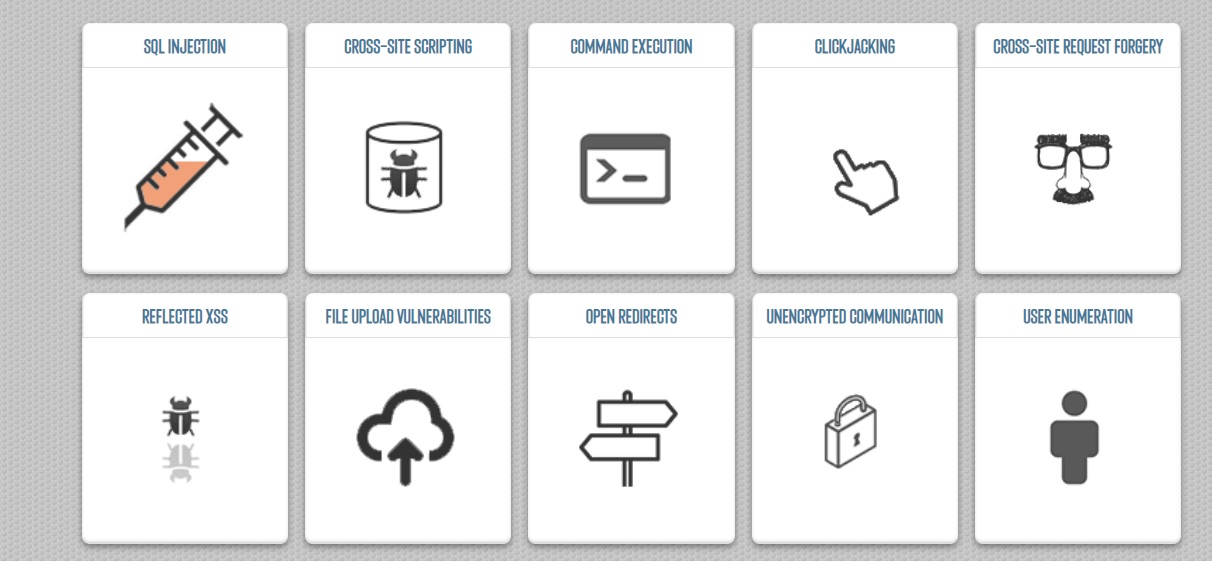
On the Hacksplaining site, in the Lessons or Lessons tab, you will find dozens of techniques or rather vulnerabilities that you can learn how to exploit, and how to find them on websites affected by these vulnerabilities. Each vulnerability has its own mechanics of detection and exploitation, and the platform will explain it to you step by step. Whether you want to master exploiting SQL Injection vulnerabilities, XSS, or the basics of Clickjacking, and others, this platform offers you all of them to learn for free. You can also register your free account on the site to access other gaps explained further.
Explanation and interactive learning in exploiting vulnerabilities
What is the best way to learn? Not watching a video or reading an article, of course, the latter helps you gain knowledge about what you are dealing with, but the real learning starts from personal experience. Subjecting that information that you gained in theory to the reality of experience, is what makes you professional in exploiting vulnerabilities and hacking in general.
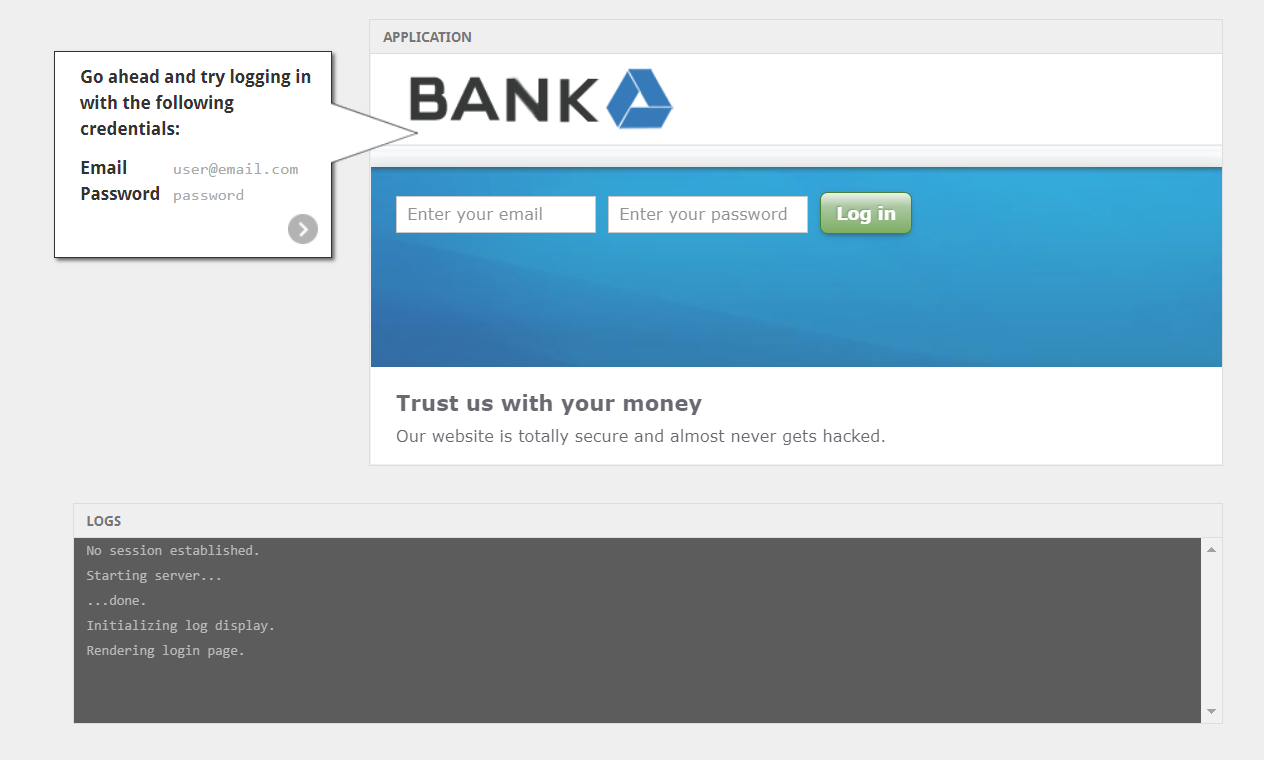
When you choose any of the vulnerabilities that Hacksplaining suggests to you, it will begin to explain it to you interactively through the experiment, telling you to click here or search for this here, and at each step it tells you the result of the actions leading to the emergence of that vulnerability. Then how to exploit it in the end before your eyes experimentally through the platform. This is the best way to learn how to deal with famous vulnerabilities and how to exploit them in hacking.
Learn to block vulnerabilities and protect your software from them
And no, the site is not evil to tell you how to exploit these vulnerabilities and then tell you to start looking for them and exploiting them to your advantage. The site is primarily intended to teach the basics of ethical hacking. Therefore, at the end of each interactive educational explanation of the vulnerabilities, the site will tell you how you can protect yourself and your software from these vulnerabilities, by explaining the causes that lead to them and how to treat them.
Of course, and again in an interactive manner, the site begins to present the reasons leading to the emergence of the vulnerability, and is it a software error in origin, or problems with server or platform updates, or various other reasons. It tells you the correct way to deal with it and protect yourself and your software from it.



















🦈🦈
Hiy
Eiar to the following link for you
Hardware hacking
I want to become a professional ethical hacker
Stvzaz
Hack bank
Melilla
2006 22 10
أريد تعلم الهاك
أوريد التعلم
Nabil
Kmlh ocpcvhjlljff
Amjad amjad1234@gmail.com
الهكر أخلق
Hacker last island of survival
Aaaaaaaaa
Aaaaaaaaa
Hola buenos, y quiero aprender
Bro quiero aprender que puedo hacer
نعم
Gracias